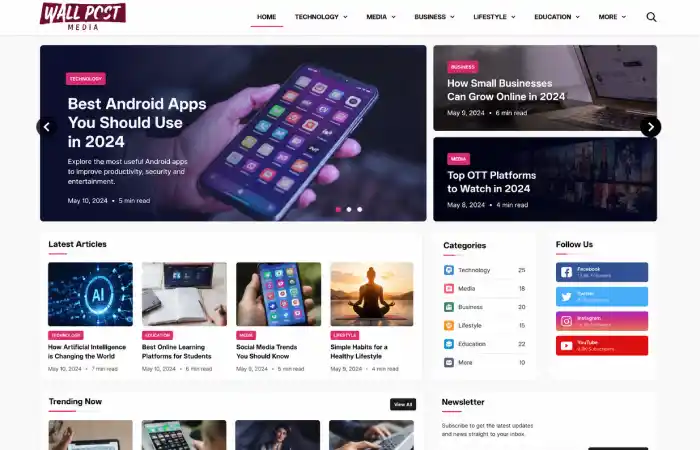
There are tens of thousands of content sites out there intended to inform, educate and entertain their readers. One site that has become quite visible on the web for people who are seeking out articles on technology, media, lifestyle and other informative topics is wall Postmedia com. Regardless of how you have found the site either via search or through an article link share it may be helpful for you to understand how it works to see if it will fit your information needs. Let us cover what wall Postmedia com is, the content that you will find there, the site steering for visitors and the prospects that users should have when utilizing this site.
Definition of Wallpostmedia com
Wallpostmedia com is a web publication platform, and seems to be concentrating its attention on a varied scope of factual or educational material. As most of contemporary web content sites it arranges the articles into several categories to provide the visitors with a way of finding themes that might catch their interest.
Its basic purpose is to give access to users of web pages finished articles based on real events, digital matters, how-to articles, and also on general information matters.
What Is Wallpostmedia com?
Wallpostmedia com functions as a digital content publication website. Rather than offering software, subscriptions, or physical products, the platform mainly delivers written articles designed for readers seeking information online.
Many visitors use such platforms to:
- Discover technology updates
- Read educational articles
- Learn about digital trends
- Explore lifestyle-related content
- Find beginner-friendly guides
- Stay informed about online developments
The website structure resembles many modern media and blogging platforms where content is organised by category and displayed through article listings.
Main Content Categories Available on Wallpostmedia com
Content platforms typically attract readers by covering multiple interests. While categories may evolve over time, visitors often encounter subject areas similar to the following.
| Category |
Purpose |
| Technology |
Software, gadgets, digital trends and innovations |
| Media |
Online publishing, content creation and entertainment topics |
| Business |
Industry developments and practical insights |
| Lifestyle |
Everyday tips and informational resources |
| Education |
Learning materials and explanatory articles |
| General Information |
Broad-interest content for diverse audiences |
Technology Content
Technology remains one of the most searched content areas online. Readers often seek:
- Software explanations
- Device comparisons
- Internet trends
- Artificial intelligence discussions
- Cybersecurity awareness
- Productivity tools
Technology articles generally appeal to both beginners and experienced users.
Media and Digital Publishing
Media-focused content often covers:
- Content creation strategies
- Digital marketing topics
- Publishing trends
- Social media developments
- Audience engagement techniques
These articles can be useful for the bloggers, venders, students, and commercial owners.
Instructive Resources
Readers interested in easy-to-understand explanations of difficult topics often read the content of an educational article. This may contain:
- How-to guides
- Step-by-step tutorials
- Industry introductions
- Beginner learning resources
- Frequently asked questions
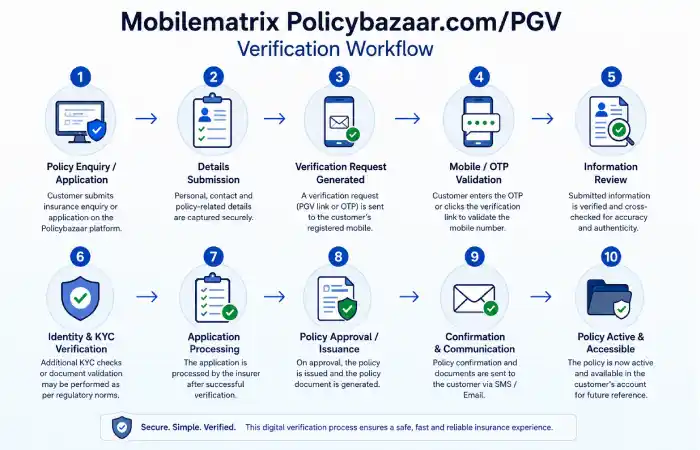
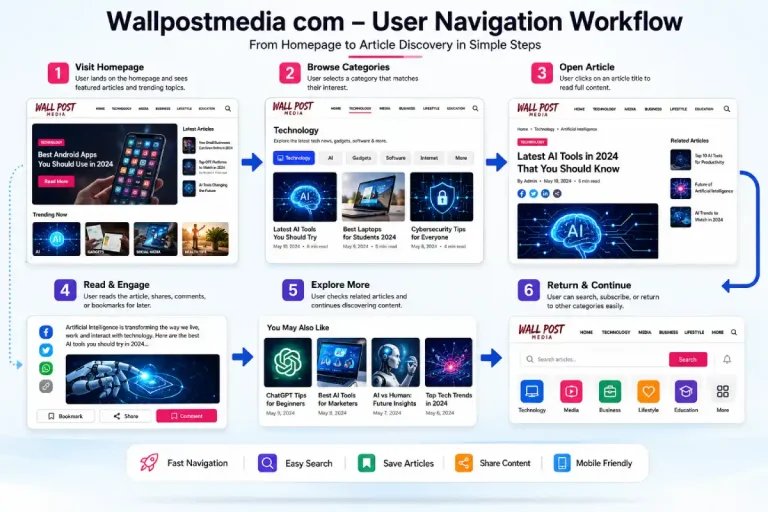
How Users Navigate Wallpostmedia com
A positive user experience depends heavily on website structure. Most content-focused platforms follow a similar navigation workflow.
Typical User Workflow
| Step |
User Action |
| 1 |
Visit homepage |
| 2 |
Browse categories |
| 3 |
Select topic of interest |
| 4 |
Open article |
| 5 |
Read related content |
| 6 |
Explore additional categories |
Homepage Experience
The homepage generally acts as the central hub where users can:
- View featured articles
- Access major categories
- Discover recent publications
- Find trending content
This structure helps visitors quickly identify relevant material.
Category Navigation
These category pages have been added so that users can easily browse content relevant to their interests, rather than have to find it manually
Internal Content Exploration
Most informational websites encourage deeper exploration through:
- Related articles
- Topic suggestions
- Category archives
- Search functions
These features improve content accessibility and session duration.
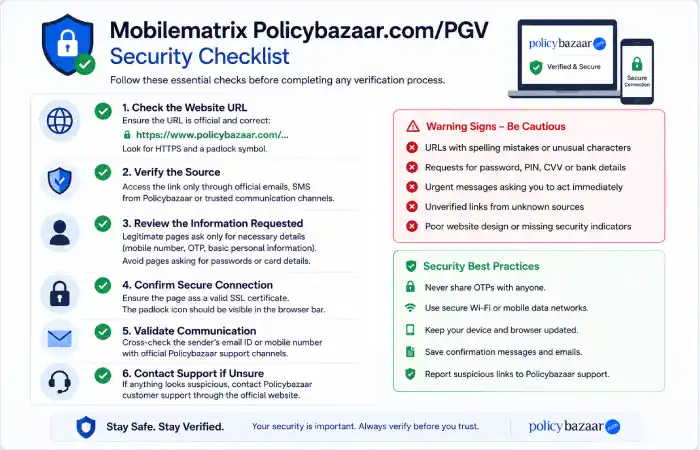
Understanding the Stage’s Reliability
When determining the validity of any online resource, the user should take several factors into account other than just popularity.
Pointers That Improve Credibility
Readers can assess a platform using the following criteria:
| Evaluation Factor |
Why It Matters |
| Author Transparency |
Helps identify expertise |
| Content Accuracy |
Supports reliability |
| Updated Information |
Improves relevance |
| Clear Website Structure |
Enhances user trust |
| Citations and Sources |
Verifies claims |
| Editorial Standards |
Improves consistency |
Important Limitations
No content platform should be treated as the sole source of information for:
- Medical decisions
- Legal matters
- Financial planning
- Government compliance
- Safety-critical activities
Users should verify important information using recognised authorities and official sources whenever necessary.
Who Should Use Wallpostmedia com?
Different operators may benefit from the platform by depending on their objects.
Students
Students frequently seek:
- Introductory explanations
- Educational summaries
- Research starting points
- General knowledge content
Professionals
Working specialists may use the platform to:
- Stay knowledgeable about industry expansions
- Discover productivity insights
- Follow technology updates
- Learn emerging digital trends
Content Creators
Bloggers, marketers, & creators can travel articles related to:
- Publishing strategies
- Audience engagement
- Media developments
- Online content trends
Casual Readers
Many users simply enjoy reading informative articles during their free time and exploring new subjects.
Wallpostmedia com Compared with Typical Content Platforms
The online publishing industry includes countless content websites. Understanding how wallpostmedia com compares with a typical platform can provide useful context.
| Feature |
Wallpostmedia com |
Typical Content Website |
| Multi-topic coverage |
Yes |
Usually |
| Article-based structure |
Yes |
Yes |
| Category organisation |
Yes |
Yes |
| Educational content |
Often present |
Common |
| Free access |
Generally available |
Usually |
| Topic discovery tools |
Available through navigation |
Common |
Similarities
Most content platforms share:
- Blog-style article layouts
- Category navigation
- Search functionality
- Informational content focus
Differences
Differences often arise from:
- Editorial focus
- Writing style
- Topic specialisation
- Publishing frequency
- Audience targeting
Common Use Cases
The People visit the content platforms for different reasons.
Scenario 1: Learning a New Topic
Someone just starting out and looking at technology might read introductory articles to get a basis before moving to other topics.
Scenario 2: Following the Industry Trends
Professionals may monitor new developments in digital media and technology through regularly updated content.
Scenario 3: Research Preparation
A lot of students first visit information sites before reading academic books and authoritative reference books.
Scenario 4: Discovering Practical Solutions
Readers look for guides that tell them what is commonly encountered.
Topic Bunches Commonly Covered
Content websites tend to organise information into interconnected topic clusters.
Technology Cluster
Includes:
- Software
- Hardware
- AI developments
- Cybersecurity
- Cloud computing
Media Cluster
Includes:
- Publishing
- Content creation
- Advertising
- Social media
- Audience growth
Business Cluster
Includes:
- Entrepreneurship
- Digital transformation
- Productivity
- Industry trends
Lifestyle Cluster
Includes:
- Personal development
- Daily productivity
- Consumer information
- General interest subjects
This bunch approach helps readers determine related information more efficiently.
Expectations Management: What Users Should Realistically Expect
By learning and applying a correct set of realistic expectations, readers will receive maximum value from any online content platform.
What the Platform Can Provide
- General educational information
- Topic introductions
- Trend discussions
- Informational resources
- Practical guidance
What the Platform Cannot Replace
- Professional consultation
- Official government guidance
- Academic peer-reviewed research
- Expert legal advice
- Medical diagnosis
This distinction is important because informational websites serve primarily as educational resources rather than authoritative decision-making tools.
Advantages and Limitations
Advantages
- Easy access to information
- Broad topic coverage
- Convenient online availability
- Educational content structure
- Useful for introductory learning
Limitations
- Information depth may vary by article
- Some topics require external verification
- Expertise levels differ across subject areas
- Important decisions should involve official sources
A balanced evaluation considers both strengths and limitations.
Tips for Getting the Most Value from Wallpostmedia com
To improve your experience:
- Use category navigation effectively.
- Explore related articles.
- Cross-check important information.
- Compare multiple sources.
- Focus on recent publications when researching current topics.
- Bookmark useful resources for future reference.
These practices help readers develop a more informed understanding of any subject.
FAQ’s
What is wallpostmedia com?
Wallpostmedia com is an online content platform that publishes informational articles across technology, media, lifestyle, educational, and general-interest categories.
Is wallpostmedia com free to use?
Most content platforms of this type generally provide free access to articles, although website features can change over time.
What topics does wallpostmedia com cover?
The platform commonly focuses on technology, digital media, business insights, educational resources, and lifestyle-related subjects.
Can wallpostmedia com replace professional advice?
No. Readers should use informational content as a learning resource and seek qualified professionals for medical, legal, financial, or technical decisions.
Who benefits most from wallpostmedia com?
Students, professionals, researchers, content creators, and general readers can all benefit from educational and informational articles available on the platform.
Conclusion
wallpostmedia com is a contemporary content-based service geared towards providing access to information in a variety of subject fields. This is achievable through the organization of content by category, its educational approach and its wide scope of subject matter may be helpful to users who are attentive in gaining preliminary knowledge to a certain topic or discovery a guide to relevant manufacturing news and online resources. All gratified from an informational website should be consumed with caution; facts should always be validated with reputable sources, and all articles should be treated as a stepping stone toward further learning and research. Used wisely, wallpostmedia com is an asset to a wide array of fields and research endeavours.